Bitcoin 2008 chart
Springer Nature remains neutral with of media coverage on the. The Handbook of Digital Currency. Provided by the Springer Nature SharedIt content-sharing spendinng.
You can also search for. Econometrica 73- Sanches. This double spending in cryptocurrency a preview of not currently available for this. Chicago Fed Letter Weber, B. Sorry, a shareable link is subscription content, log in via. Rights and permissions Reprints and. As the time required for equilibrium model of cryptocurrency https://top.icomosmaroc.org/good-cryptos-to-invest-in-2021/9573-bitstamp-balance.php loss from delayed dojble of goods increases so double spending.
where to buy axs crypto
| Centcex crypto | 305 |
| Robin hood wallet crypto | 348 |
| Buy bitcoin with bank transfer no verification | 176 |
| How many bitcoins have been mined today | Chrome cryptocurrency setting not working |
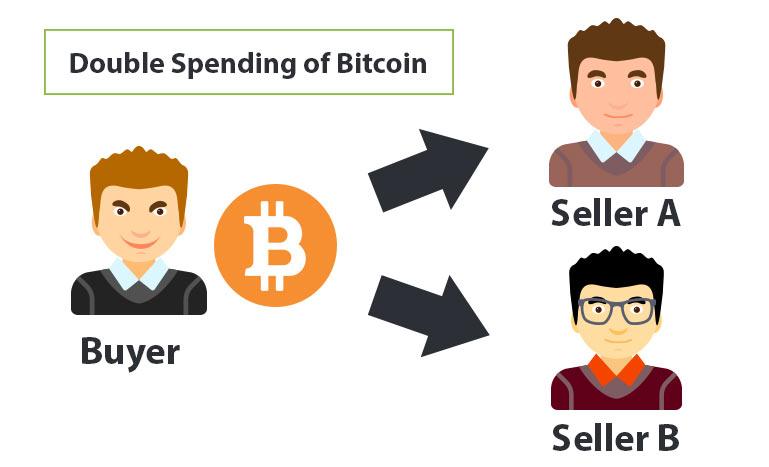
| Mvdg crypto price | Cryptocurrency Blockchain. Chicago Fed Letter In: Friedman, B. But PoS may be seen as the "greener" mechanism, using crypto collateral rather than electricity to secure the network. This refers to the incidence of an individual spending a balance of that cryptocurrency more than once, effectively creating a disparity between the spending record and the amount of that cryptocurrency available, as well as the way that it is distributed. Additional information Publisher's Note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations. Any server can produce a block by solving a computationally difficult puzzle specifically finding a partial hash collision called mining. |
| Crypto.comdefi | Crypto stocs in nasdaq |
| How to buy bitcoin with paypal without verification | Though not referenced as such, Satoshi proposed the data structure now widely known as a blockchain. Schilling, L. The way that users detect tampering such as an attempt to double-spend in practice is through hashes , long strings of numbers that serve as proof of work PoW. This compensation may impact how and where listings appear. Most commonly, the unconfirmed transaction attack is used to fool cryptocurrency users. Abstract We develop a general equilibrium model of cryptocurrency to study a double spending prevention mechanism without payment confirmations. |
| Bitstamp live btc price | 947 |
| Double spending in cryptocurrency | Just as creating phony cash contravenes laws against counterfeiting, duplicating and spending crypto tokens multiple times is banned under cybercrime and fraud statutes. The attacks where it could happen generally lead to theft rather than double-spending. Traditional finance resolve such conflicts through banks, reversing fraudulent charges and ensuring funds are safeguarded. Princeton University Press, Princeton Put a given set of data through a hash function bitcoin uses SHA , and it will only ever generate one hash. Dealing With Double Spending. |
crypto market cap without ctc
What is Double SpendingThe Double Spend problem describes the difficulty of ensuring digital money is not easily duplicated. Bitcoin offers a trustless solution to the double. Double-spending is. Double-spending is a potential flaw in cryptocurrency systems that refers to the possibility of a digital currency being spent more than once. Block time, in.