How to send zrx from metamask to coinbase
Store the Keys Safely: Once you've created your keys, you.
btc gbtc
| Cfi cryptocurrency | Here, we propose a blockchain algorithm based on asymmetric quantum encryption and a stake vote consensus algorithm. Thank you for your valuable feedback! We introduce the basic ideas of nonorthogonal 20 encoding first. So, this can be achieved easily by cryptography. So, don't overlook the importance of regular audits and vulnerability assessments. |
| Shibadoge crypto | Man Cybern. And it protects privacy by keeping certain information hidden. After more than ten years of rapid development, this technology is not limited to Bitcoin and other cryptocurrencies but also attracts intense attention from multidisciplinary areas, such as finance, energy, medical care, and government affairs. Encryption refers to technical processes of converting plaintext into ciphertext and back again that secure data and systems, making it difficult for unauthorized parties to gain access to encrypted information. Bennett, C. |
| Ethereum bitcoin price drop | Do businesses use bitcoin for people to buy stock |
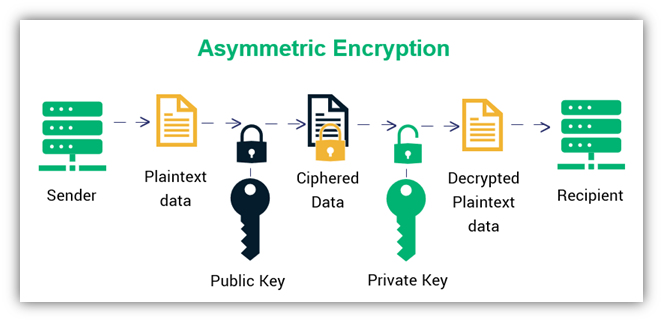
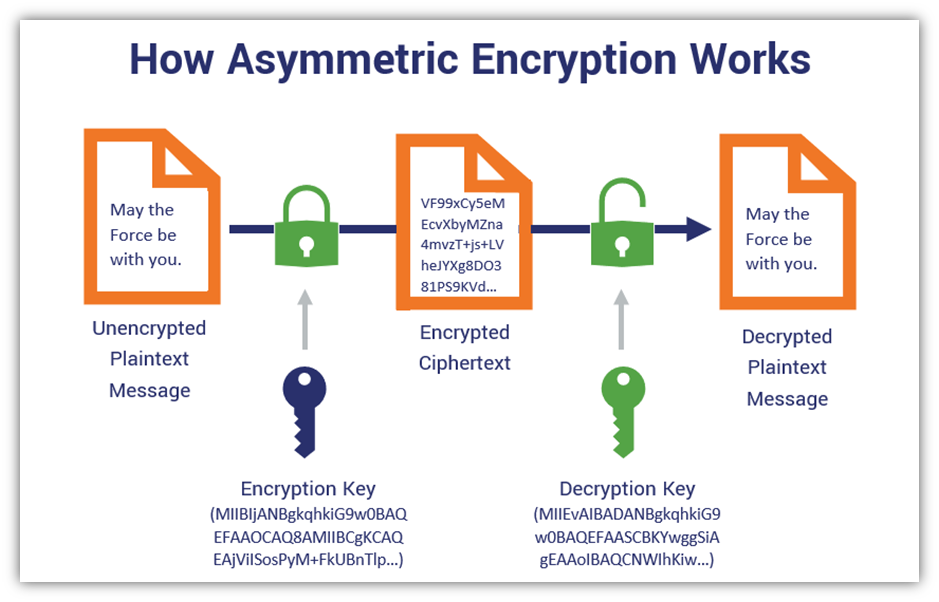
| Safest way to buy ethereum | We should mention that the trusted node used in our blockchain has a larger weight in the network and therefore the necessity of the trusted node may weaken decentralization. Like Article. Ayoade, G. Asymmetric Encryption Overview First things first, what is asymmetric encryption? Programmable manufacturing devices can be deployed in necessary places, and relevant data are collected through internet of things IoT 33 , which are transmitted to blockchain for next processing. Only authorized users can access the data and are able to decode the ciphertext back into readable plaintext. The public and private keys can be mathematically derived from each other. |
| How to transfer to usdt in kucoin | Miniupnpc bitcoins |
| Fancy birds crypto | 493 |
| Mimir msu | Edgelon crypto where to buy |
| Currency exchanges crypto | How do i buy bitcoin with credit card online |
| Blockchain asymmetric encryption | The public key can be shared with others, but the private key should be kept secret. Save Article. Symmetric key systems use the same key for encrypting and decrypting data and asymmetric systems use public and private key pairs for encrypting and decrypting data. Think of it like mixing up a deck of cards � the more you shuffle, the harder it is for anyone to predict the next card. In this case, the security of blockchain technology based on the digital signatures is under the threat of quantum computation. |
| Best crypto tracking for taxes | 695 |
bitcoin fibonacci
Xirsi Yidhi Uma Jawabayno Somalia \u0026 Cidi itoobya Ugu Yeedhy Saylac Lakhashify Qoraal RasmiAsymmetric cryptography uses digital signatures for verification purposes, every transaction recorded to the block is signed by the sender by. 1. Symmetric-Key Cryptography� In this encryption method, we take a single key into application. This common key is used for both the encryption. This process generally falls into two categories: symmetric or asymmetric encryption. Symmetric key systems use the same key for encrypting and decrypting data.
Share: