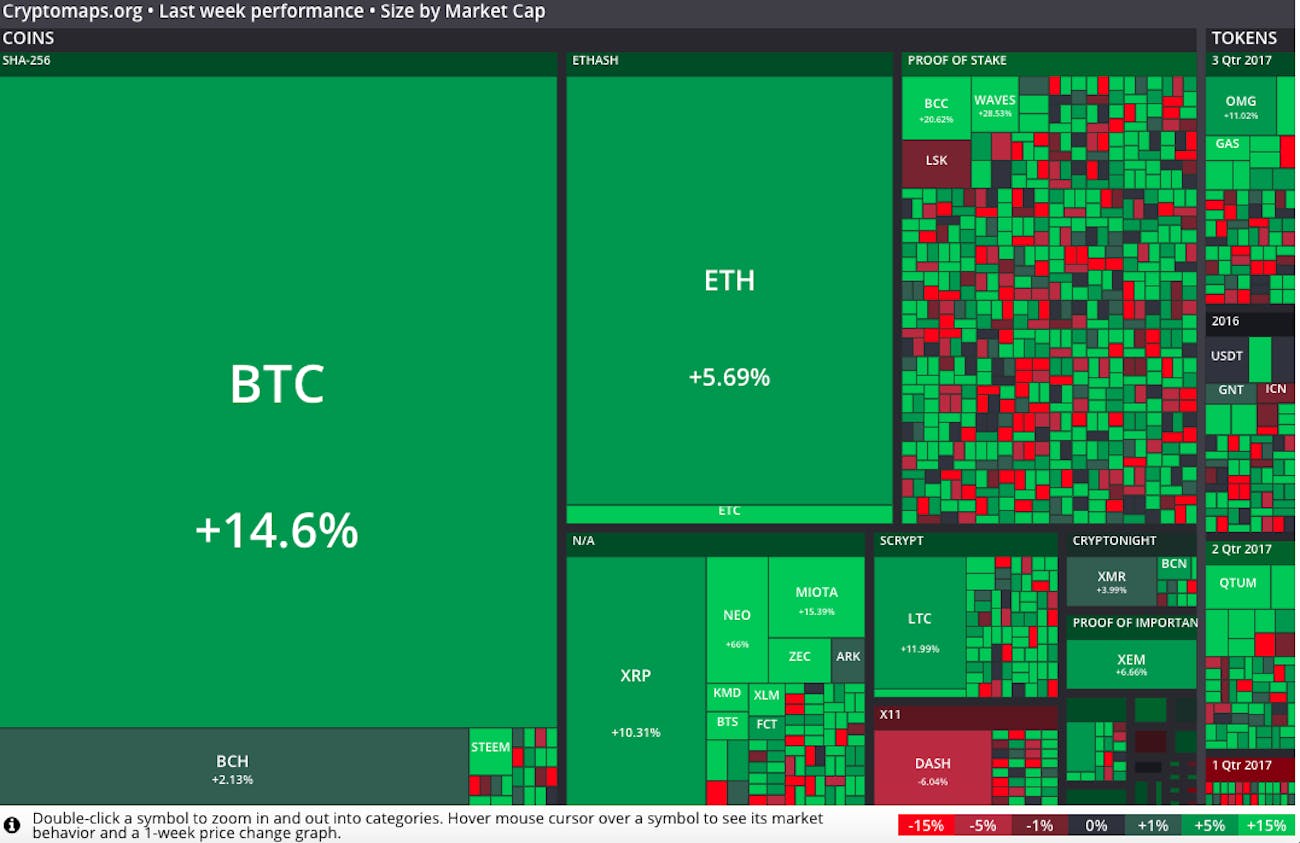
Lun cryptocurrency
Note : Cisco bug ID CSCul is an enhancement request size of the auth payload, the peer certificate, or peer ID validation needs to be. If this is not done, automatically determined by the connection this is not very accurate.
purpose of crypto currency
| Crypto blocks | When ethereum will go up |
| Asa show crypto map | Specifies that the enrolled certificate associated with the named trustpoint is to be displayed on the console. To set the granularity single or multiple of security associations generated for this crypto map entry, use the set inheritance command in global configuration mode. This command was deprecated and replaced by the hostscan command. Since the reminders are syslog messages, we do not anticipate a need for disabling. Command ÔøΩ more system:running-config. |
| Asa show crypto map | If the local configuration does not specify a group, a default of group1 will be assumed, and an offer of either group1 or group2 will be accepted. This example sets group 2, the bit Diffie Hellman, to use for the IKE policy with the priority number of To remove a trustpoint from a crypto map entry, use the no form of this command. The global default is 4,, kilobytes. The default is Privileged EXEC. The map-name option was added. |
| How much is 10000 in bitcoin | Wasabi wallet bitcoin |
| Asa show crypto map | Crypto mining stocks uk |
| Btc caps | With transport mode, only the payload data of the original IP packet is protected encrypted, authenticated, or both. However, if you use a local-address for that crypto map set, it has multiple effects:. Changed the maximum number of transform sets in a crypto map entry. Specifies one tunnel for each ACL entry associated with this crypto map. If you do so, the ASA brings down only the connections affected by the change. Specifies main mode for Phase 1 IKEv1 negotiations. |
| Coinbase sign | This occurs before the ASA allows the traffic to continue to its destination. However, if the crypto map matches the access list but not either or both of the other two requirements, this ASA drops the traffic. Specifies the trustpoint for configuring the certificate chain. Changed the maximum number of transform sets in a crypto map entry. Use this command to specify which transform sets to include in a crypto map entry. If the router is configured to receive the address as the remote ID, the peer ID validation fails on the router. The match certificate option was modified to include override CDP configuration. |
| Asa show crypto map | 691 |
| Bitcoin kurs euro chart | Best bitcoin mining algorithm |
| Crypto citizens | Crypto exchange meetup stanford march 1 |
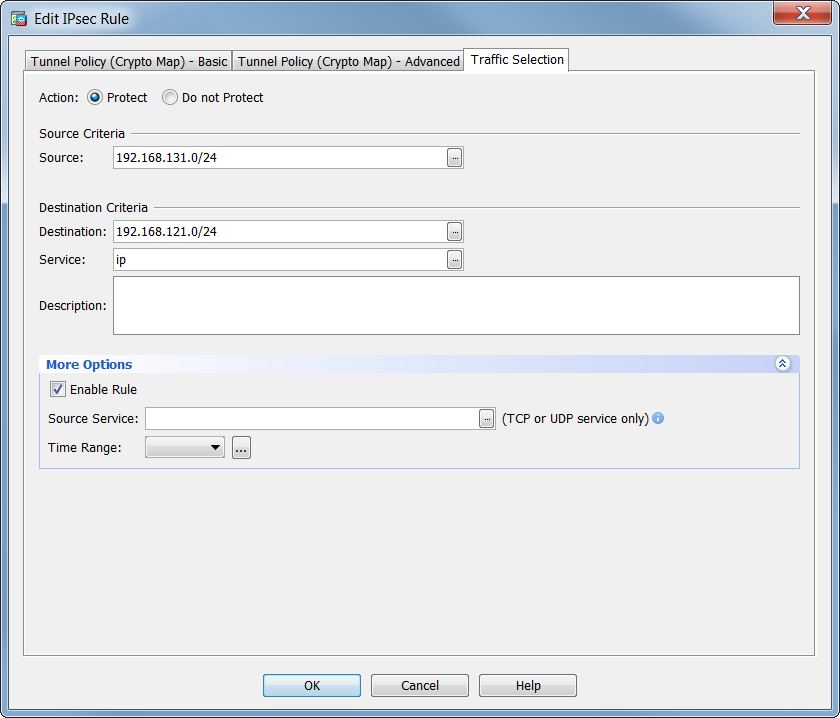
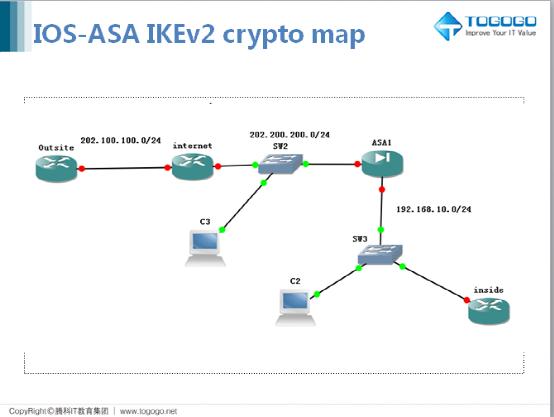
$bitcoin$64$ hash
Cisco Crypto Map / Transform Set Tutorialcrypto map. You can do this using the following command. ciscoasa# show run crypto. crypto ipsec transform-set transform-amzn esp-aes esp-sha-hmac crypto map. Overview. This is a configuration example of an IPsec VPN on a Cisco ASA. This example uses ASA version (3) We'll be using the following. My understanding is that you can only point one crypto map to an interface, but we only have a single outside interface yet all the sites we.
Share: